The SMSI Inc. Security Solution Hierarchy provides a logical model from which to build a cost-efficient Security Program. At SMSI we advocate “Outcome Based Decision Making.” This means that as you evaluate and existing security program or initiate a new security two fundamental steps must be taken.
Step 1: Conduct a thorough Vulnerability/Risk Assessment. Security programs must be need. Remember that security is a situational discipline which means every security program is unique.
Step 2: Applying the principal of Outcome Based Decision Making (OBDM) the security professional must determine the intended outcomes and goals of the intended security program. Once those goals have been articulated, it is time to determine how to best achieve those objectives.
This is where the SMSI Inc. Security Solution Hierarchy comes into play. The Security Solution Hierarchy provides a logical construct for building an effective security program. The Hierarchy encourages the application of lower cost remedies first. Once those lower cost remedies are in place, the security professional than must determine what vulnerabilities remain, given the ambient threat environment.
Level two of the Hierarchy applies CPTED remedies, and electronic systems such as video surveillance systems with video analytics, access control systems and possibly man-traps. This is the point at which more traditional physical security devices are applied.
If the site being considered is still on the drawing board, CPTED should be applied at level one.
Level Three is the most costly because it involves the use of security personnel. However, if due diligence is applied at levels one and two, level three will be that much more effective.
 The Security Solution Hierarchy, (SSH), provides a logical construct for building a cost efficient security program. This hierarchy is loosely modeled after Maslow’s Hierarchy of Needs. If you remember, Maslow’s Hierarchy was a model based on prepotent needs. In other words, if the needs at the bottom of the pyramid were not satisfied, the need at the top of the pyramid really didn’t matter.
The Security Solution Hierarchy, (SSH), provides a logical construct for building a cost efficient security program. This hierarchy is loosely modeled after Maslow’s Hierarchy of Needs. If you remember, Maslow’s Hierarchy was a model based on prepotent needs. In other words, if the needs at the bottom of the pyramid were not satisfied, the need at the top of the pyramid really didn’t matter.
SSH provides a model for the decision making process. First determine the desired outcomes for the security program under consideration, the then prioritize the strategies to produce those outcome. If you follow the Security Solution Hierarchy, using the Maslow model, the security professional is prompted to first come up with low cost solutions first. After low cost solutions are initiated, in some case those solutions may be sufficient. If they a not adequate, than move to the CPTED/Electronic level (one could make a case for putting CPTED at level one). We placed CPTED in the second level, because some CPTED remedies can be costly such as effective lighting. However, many CPTED strategies have very little budgetary impact.
It is not unusual to find organizations that turn this Hierarchy upside-down, where the first choice in to hire security personnel. We encourage security managers to build their own Security Solution Hierarchy that fit their own unique set of needs. SMSI applies this model to all of our consultation clients. This model works for almost any vertical.
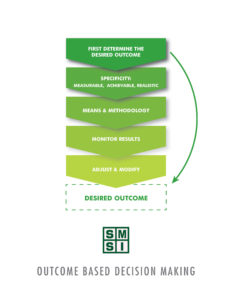
Outcome Based Decision Making
Outcome Based Decision making is a simple concept, but often missing from the decision making process. Stated simply, before deciding to hire security officers, put in an alarm system or install a video surveillance system, catalog the actual outcomes you expect the security program to produce. All to often we assume the application of various security methodologies will magically result in a sound security program, and later discover, not so much.
SMSI Inc. provides the expertise and support to guide our client through the security solution Hierarchy and the Outcome Based Decision making process by ensuring that each component of the your security program is need driven and capable of providing measurable results.
