WORKPLACE VIOLENCE MITIGATION Regulations Should Not Be The Sole Driver of Hospital Security Programs: Good security is just good business.
As posted on LinkedIn Pulse on November 29, 2016
The Workplace Violence Mitigation for Hospitals
The Graphic above depicts a composite image of Urban & Rural Hospitals as a continuum.
Here in California, Workplace Violence continues to receive major attention by the California Legislature, as an adjunct to the California Health & Safety Code. Also, the California Occupational Safety and Health Act of 1973, imposes safety responsibilities on employers and employees, including the threat, and mitigation of WPV.
Additionally, OSHA has acknowledged the implicit security risks for hospitals in their publication: Guidelines for Preventing WORKPLACE VIOLENCE for Healthcare & Social Service Workers. More recently, the United States GAO published WORKPLACE SAFETY & HEALTH: addressed the security concerns of the healthcare industry. The publication also spoke to the additional efforts needed to Help Protect Health Care Workers from Workplace Violence.
The accumulated import of these publications, coupled with today’s dynamic threat environment, the adequacy and efficacy of healthcare security programs is in a state of transitional adjustment. These publications, as well as accumulative data, indicate that the threats to patients, as well as employees, and invitees is both internal and external challenge.
The accumulative impact of these efforts, along with the potential impact of premises liability, fueled by charges of inadequate security, and/or related intentional torts, we have a persuasive rational for reasonable mitigation before the fact. The exposures may also include worker’s compensation claims. On the premises liability side of the equation, it is important to remember that contracted employees are not limited to worker compensation redress. Contracted employees have, and continue to bring civil actions against healthcare providers.
There is a plethora of potential mitigation strategies. Because security is a situational discipline, meaning “one size does not fit all,” the first logical step for developing a mitigation strategy is a comprehensive security assessment.” This assessment must quantify both the internal and external threat environment. No two facilities have the same defined threat environment. This means that no two hospitals are amenable to the same set of remedies.
Over the years, the security tool bag offers more options than ever before from training to state of the art technology. Over the past 20 years’ security technology has significantly evolved, placing less reliance on payroll burden, a greater level of employee participation as part of the solution. Not only has technology evolved, it has become much more cost effective, especially video surveillance systems, in terms of cost and monitoring options.
There are significant opportunities to enhance any security programs through the efficient application of CPTED (Crime Prevention Through Environmental Design). CPTED is very cost efficient and it encourages behavior modification solutions. The concept of CPTED acknowledges that successful security programs are contextual and are heavily affected by how each program is perceived. CPTED has the potential to affect perception in a positive and productive way. Conversely, the absence of CPTED may diminish the impact, of an otherwise, well-conceived security program.
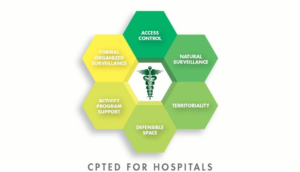
For better or worse, it is just a matter of time before these standards here in California will help to define a reasonable standard of care nationwide. Periodic comprehensive and objective security assessments may help to mitigate problems down the road. Most security assessments also discover opportunities for cost-effectiveness. As previously alluded to, CPTED is but one of those cost beneficial strategies that is often overlooked.
Bottom-line: Having an, effective security should not be driven by regulation alone. An effective security program is cost-effective and it should deliver demonstrable ROI. Effective security programs will protect property, as well as inventories. It will mitgate workplace violence. With today’s technology, there is less reliance on payroll burden. For those that apply CPTED strategies, the result will be a security program where to whole is greater than the sum of the parts.
The model for an effective Hospital security program, is embodied if the Security Solution Hierarchy.

This model depicts various levels of security predicated on need and cost consideration. The Hierarchy, as depicted here, is intentionally disjointed. Because each level is driven by need, starting from the bottom up, all levels may not be required depending on the need/threat environment. These determination should be the subject matter of a thorough needs assessment.
William H. Nesbitt, CPP, Certified CPTED Practitioner; bill@smsiinc.com
President: SMSI Inc. (Security Management Service Internationals, Inc.
805-499-3800, Thousand Oaks, CA
