CPTED – A Unifying Force For Hospital Security
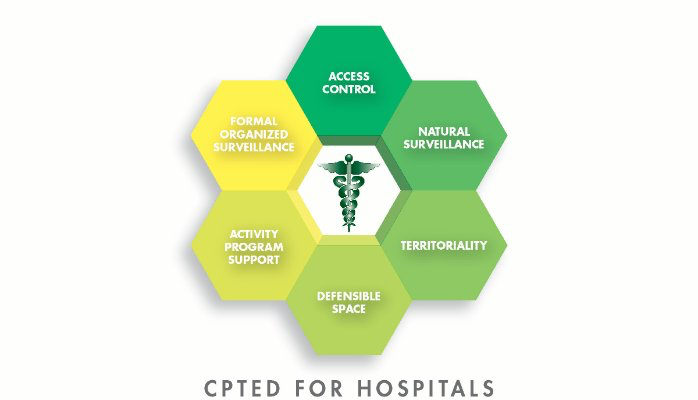
If there is one industry that is well suited to the application of the principals of CPTED (Crime Prevention Through Environmental Design), it is the healthcare community, including hospitals, urgent care centers, walk-in clinics, drug treatment centers and behavioral health facilities. All, of these facilities are characterized by the relative ease of access, both at the perimeter as well as internally. The basics of CPTED include Natural Surveillance, Natural Access Control and Natural Territorial Reinforcement.
Obviously, the best time to apply CPTED principals is during the design phase of new construction. However CPTED principals can readily be applied to the “built environment.” The application of CPTED principals will significantly enhance the benefits derived from all of the more traditional security methodologies such as access control systems, video surveillance systems and the application of security personnel. Clearly CPTED facilitates the ability to do more with less.
As with most security programs, the mission of hospital security programs is to reasonably protect people, property and information. The very highest standard of care is applied to the protection of patients. The insertion of CPTED into the conversation will ensure that the totality of the security program is greater than the sum of the parts.
In previous publications we have drawn attention to the integral role that perception plays in all effective security programs. Despite reality, security programs that are perceived as laisse-faire are generally less effective than those security programs that are perceived effective and well designed. The result is deterrence.
Those security programs that are routinely ignored, by would-be perpetrators, significantly increase liability. Those would-be perpetrators may be representative of both internal and external threats. When security breaches become the rule, as opposed to the exception, security litigation I is waiting just around the corner.
To give CPTED some relevant context, imagine two urgent care centers, 1 & 2. UCC #1 has an ill-defined property-line, the shrubbery is not well trimmed, some exterior lights are out of service and the parking facilities are available for anyone in the neighborhood. There is no signage directing visitors and customers where to enter the building, and where to go once inside. The general housekeeping gives the perception of neglect.
On the other hand UCC #2 is well maintained, the shrubbery is trimmed and low to the ground offering wide field of views. The exteriors are well illuminated with LED luminaries. Employees within the clinic have the ability to obverse exteriors and visitors are guided to acceptable points of ingress both at the perimeter as well as within the clinic.
Which of the two clinics is more likely the target of criminal activity. Albeit, the example is simplistic, but it is intended to make one aware of a very cost-efficient strategy that will significantly enhance the ROI of any security program. CPTED will make any security program better. CPTED can be applied at almost every level of the hospital/clinic security program, both externally and internally. It can be applied to food service, environmental service, pharmacies and materials management. It can be applied to L&D, medical surgical floors, EDs and parking structures.
If CPTED principals are inculcated into the security design of healthcare facilities, the overall impact of traditional security methodologies, such as video surveillance, lighting, access control systems and security officers will be significantly increased. CPTED is quickly becoming the reasonable standard of care.
We have been using the graphic depicted below, the Security Solution Hierarchy, for a number of years. We recently modified this Hierarchy. Because of the foundational importance of CPTED, we have placed CPTED, at the first level of the Security Solution Hierarchy because CPTED will ensure that all subsequent strategies are more impactful. In other words, we advocate that CPTED should provide the fundamental blueprint on which the entire security program is built.
We believe that the best opportunity to apply CPTED security design is after a through security assessments. Obviously, the best opportunity for the application of CPTED principals is during the initial planning phase during new construction. However CPTED can also be effectively applied to the built environment also. CPTED will also ensure cost efficiency through demonstrable improved ROI.
 Clearly this model can be applied to any security and loss prevention environment. However CPTED is particularly effective when applied to those verticals that provide access to the public, such as schools and universities, shopping malls, high-rise office buildings and sports/entertainment venues. As stated earlier, if CPTED has not been applied as part or the new construction strategy, the second best opportunity, is to apply CPTED in the wake of a through impartial security audit by a qualified security professional. When CPTED is applied to any security operation, it will immediately increase the real value of the security program in a measurable way.
Clearly this model can be applied to any security and loss prevention environment. However CPTED is particularly effective when applied to those verticals that provide access to the public, such as schools and universities, shopping malls, high-rise office buildings and sports/entertainment venues. As stated earlier, if CPTED has not been applied as part or the new construction strategy, the second best opportunity, is to apply CPTED in the wake of a through impartial security audit by a qualified security professional. When CPTED is applied to any security operation, it will immediately increase the real value of the security program in a measurable way.
For those who believe security requires a team effort, CPTED has the potential of defining the game plan. CPTED will help to ensure that the security program will gain favor with the C-Suite, in part, because CPTED is very cost efficient by enhancing the ROI of any security budget. CPTED enhances the image of the affected organization in a manner that gains favor with the public being served. Remember, security is a situational discipline. This means the CPTED programs are also situationally determined.The most successful CPTED programs are the product of comprehensive security assessment.
As usual, we welcome your input and comments. For those of you who have anecdotal commentary in the use of CPTED, feel free to share your thoughts. It is my belief that the application of CPTED principals to any security program, will make it better.
William H. Nesbitt, CPP bill@smsiinc.com www.smsiinc.com
President: Security Management Services International, Inc.
Member of ASIS International, IAHSS, ASHRM & ACHE
Join Security Source Online here on LinkedIn